"Model your defenses, secure your future"
System modeling is a valuable tool for cyber defense, providing a comprehensive understanding of the components, processes, and relationships within a system. System modeling allows organizations to anticipate potential threats, mitigate them, and respond to them more effectively. Modeling in general, and system modeling in particular, has been shown to inform the organization in two ways. First, the process of modeling enhances understanding of the system and its interaction with the organization. Second, models provide the basis for analysis. In this blog post, we discuss the key benefits of system modeling for cyber defense.
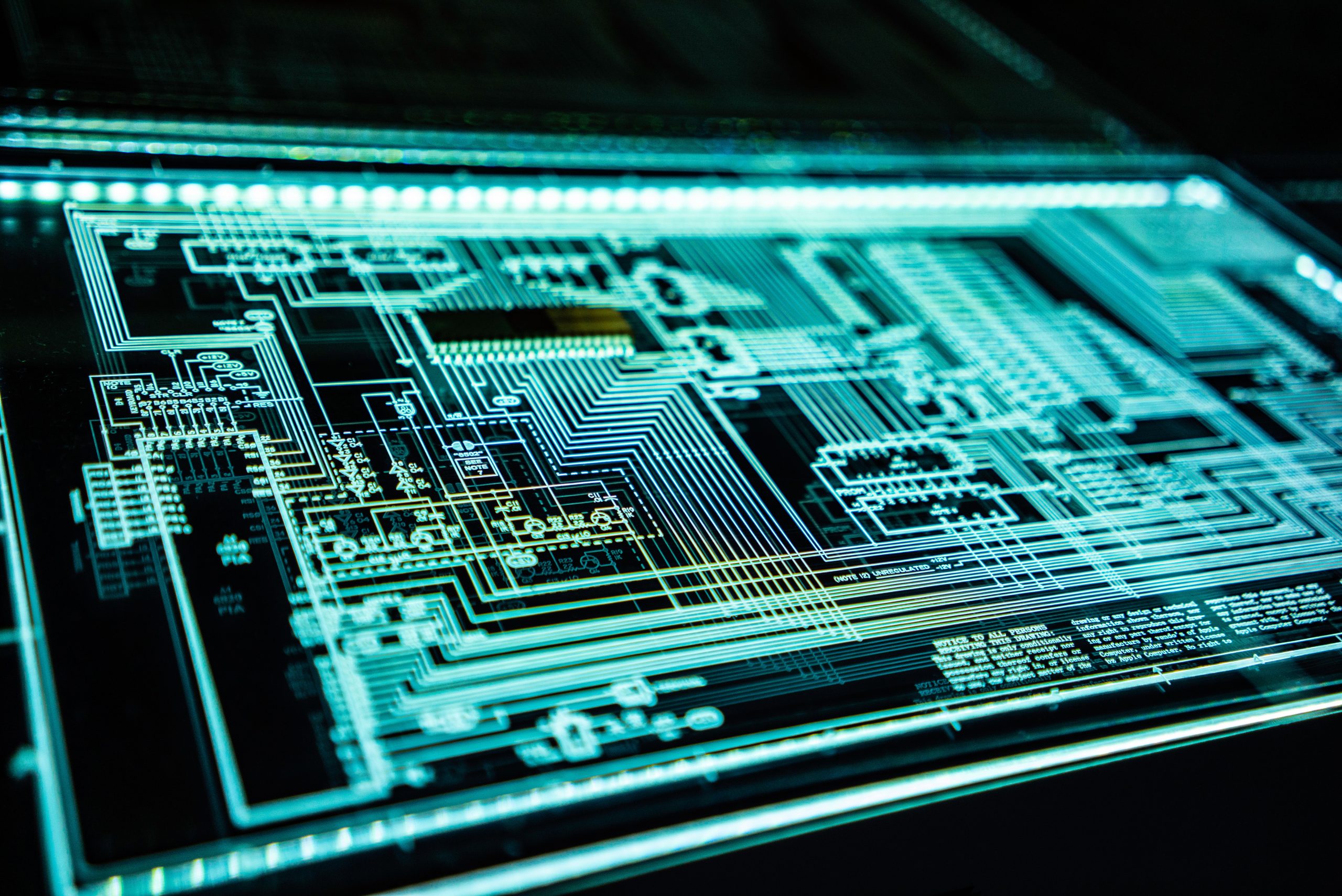
- Improved Situational Awareness: System models provide a visual representation of the system and its components, which enhances situational awareness and enables organizations to identify critical assets, interdependencies, and potential points of failure. This information is crucial for developing effective cyber defense strategies and ensures that resources are deployed to the areas that need them the most.
- Threat Anticipation: By understanding the system architecture, organizations can anticipate potential threats and vulnerabilities. System modeling empowers organizations to identify and assess new situations, enabling the identification of weak points and determination of the impact a potential threat could have on the system. System modeling allows organizations to take proactive measures to prevent or mitigate anticipated threats.
- Faster Incident Response: System modeling provides a clear understanding of the system and its components, which enables organizations to respond to incidents more efficiently. In the event of a security breach, organizations can quickly identify the source of the problem, assess the damage, and take appropriate action.
- Improved Collaboration: System modeling helps organizations collaborate effectively in the face of cyber threats. By having a shared understanding of the system architecture, different departments within the organization can work together more effectively to address security issues. This can lead to more coordinated and efficient incident response and recovery efforts.
- Better Resource Allocation: System modeling enables organizations to prioritize and allocate resources more effectively. By understanding the critical components and processes within the system, organizations can focus their resources on the areas most likely to be impacted by a cyber attack, ensuring that they are better prepared to respond.
In conclusion, organizations should be taking advantage of the benefits of system modeling because it is a valuable tool for cyber defense. By providing organizations with improved situational awareness, faster incident response, better collaboration, and improved resource allocation, system modeling enhances cyber survivability. Well-constructed, comprehensive system models can reduce exposure to cyber threats and increase the organization’s ability to respond effectively in the event of an incident.